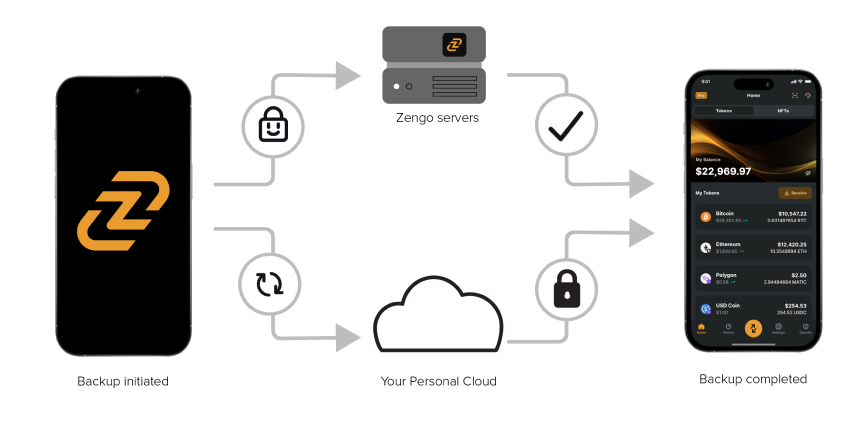
At Zengo, our mission is to provide users with a superior user experience that enables our users to simply and securely manage their crypto assets while eliminating the typical risks associated to private key management and account recovery.
Unfortunately, replacing a recovery phrase with a password isn’t going to solve this problem, as both can be lost or forgotten, leaving funds locked in wallets and lost forever. We saw this as a central problem preventing the mass adoption of crypto assets and we set out to solve it.
Therefore, we’ve made a bold move and made Zengo completely password free using a security architecture that utilizes multiple security layers and factors, while keeping the user experience straightforward and consistent.
One of the security factors central to our solution is biometric 3D face authentication. Since our private beta launch, we have received quite a few excellent questions about our use of biometrics and why they are both a critical and ground breaking feature of the Zengo wallet. This post is dedicated to explaining why Zengo needed biometrics for complete user security and recovery, why we chose the specific technology we did and how it was implemented.
Biometric Face Authentication
Biometric authentication eliminates many of the problems with traditional passwords. When implemented correctly, biometrics make identity theft attacks much harder and identity loss cases much rarer while offering a superior user experience — anyone can use your password/private key but only you can use your Biometric authentication.
That is the reason why leading consumer electronics companies such as Apple and Microsoft are using biometric face authentication as the main authentication factor for their newest products.
Challenges arise with on-device biometrics when the original device is no longer accessible, if for example it was lost or stolen, or simply never had native support for biometrics included when is was built. In these scenarios, the user authentication must take place on Zengo’s servers and not locally on the device. Therefore, although we do use the on-device authentication (i.e. Apple’s TouchID and FaceID) an a convenient security layer, those solutions are not feasible for account recovery when the original device is no longer in the user’s possession.
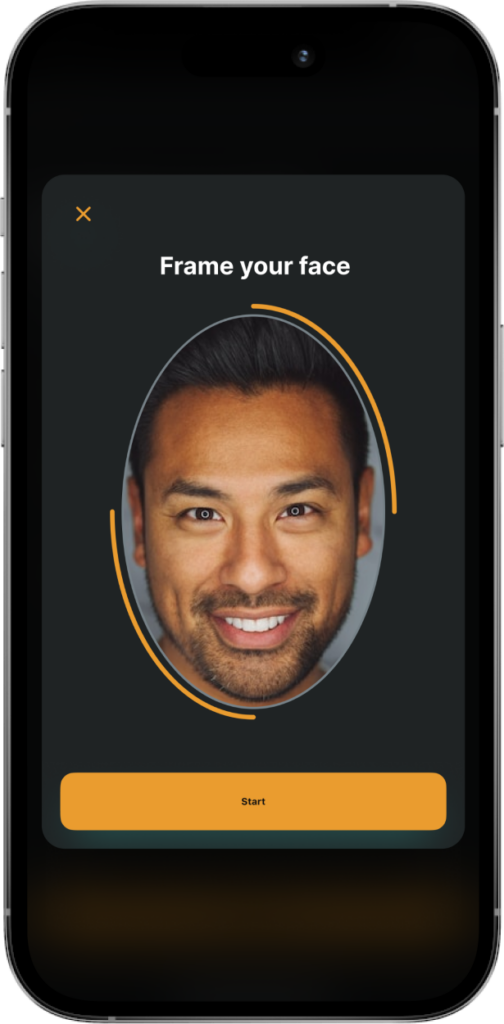
ZoOm in Action (source)
To guarantee that our users can always use their biometrics to recover their accounts, we have partnered with FaceTec to integrate the ZoOm® 3D Face Authentication solution into our mobile app and server. FaceTec technology has been developed over the last 5 years in the USA and used in the financial domain by banks, sharing economy providers and many others. Not to be confused with the conventional “Facial Recognition” that is typically used for surveillance and law enforcement, FaceTec provides biometric authentication software that protects user privacy and secures their accounts. The FaceTec solution is specifically tailored for the consensting user authentication and never involved in the ethically questionable mass surveillance domain.
Security
Biometric authentication eliminates many of the problems of traditional passwords, but can bring new vulnerabilities such a spoofing. Spoofing is when a bad actor uses photos, videos or masks that look like the User to fool the system into providing unauthorized access. The key to thwarting these attacks is a concept called Liveness Detection. This technology determines if the biometric data being presented to the sensor is being captured from a real human being. When Liveness Detection is truly robust to spoofing attacks all of the benefits of biometric authentication can be realized, and the User cannot be impersonated, and the biometrics credentials can’t be forgotten, phished or stolen.
The security of Zengo’s biometric authentication is based on ZoOm’s security. ZoOm is publicly Certified (iBeta/NIST ISO 30107-3 PAD Level 1&2) for correctly identifying users and resisting many sophisticated spoofing attacks.

ZoOm certifications (source)
FaceTec’s solution is in production on 5 continents, and was designed, tested at scale, and certified to withstand the kinds of spoofing and masquerading attacks that biometric authenticators see in the wild by validating the three-dimensional liveness of the user.
- 2D paper photos & digital images
- High resolution videos
- Image swap-in after liveness check
- Paper masks with eye & mouth cutouts
- Hollywood masks, wax figures & lifelike dolls
- Photos or video frames animated into avatars
- Video projections on 3D heads
- Sleeping users with closed eyes
- Impostors, lookalikes & identical twins
List of spoofing attacks not bypassing ZoOm (source)
What this means is that the system cannot be spoofed with a high-resolution picture, video, or even a 3D mask (“Mission Impossible style”).
ZoOm face authentication was tested against Holywood-style masks
But please, don’t need to take our word for it. We encourage you to test the system for yourself by trying to restore your account with a picture or video of your face. It will fail, and you can rest assured those pictures of you on Facebook won’t unlock your Zengo account.
You can check out this short video showing testing at the FaceTec spoofing lab to see how secure the system is against advanced spoofing attacks.
If you are interested in learning more about the security of the ZoOm solution, please check out the following resources from the ZoOm website:
- https://www.zoomlogin.com/wp-content/uploads/2018/09/FaceTec_Liveness_Testing_Methodology.pdf
- https://www.zoomlogin.com/wp-content/uploads/2018/11/ZoOm-Customer-Internal-Testing-Guidance.pdf
- https://www.zoomlogin.com/wp-content/uploads/2018/11/FaceTec_PAD_Testing_Whitepaper.pdf
Privacy
As a privacy-conscious user, you are probably wondering who can see your pictures? The simple answer is: no one.
FaceTec cannot see your pictures as all of the visual information is processed within the Zengo servers and never leaves them.
Zengo cannot see your pictures: The Zengo app cannot understand any of the data it communicates between ZoOm’s software elements. All of the communications are encrypted and encoded as a ZoOm proprietary FaceMap and are unreadable by Zengo. The information is only decoded and decrypted by the integrated ZoOm technology to confirm whether the 3D face image data represents the same person as is enrolled in the previous FaceMap.
Additionally, the FaceMap data is securely sent and stored in an encrypted manner. When stored, some of the required information from the FaceMap format is removed by ZoOm, so that FaceMap can only be used for comparison but not for authentication.
At Zengo we adhere to privacy regulations such as GDPR and apply the right to be forgotten, relevant to all biometric data.
Conclusions
With Zengo, we use biometrics-based authentication instead of passwords, as one of our key security factors. Biometric-based authentication brings a new set of advantages, but also new vulnerabilities and privacy concerns. That is why we have carefully constructed our biometric system to provide the most security with the least impact on customer privacy.
We support the native device biometrics, but that is not enough, as some scenarios require biometrics to be used across devices.
To ensure the best result for our users, we integrated the best-in-class server based face authentication solution with native phone biometrics. Additionally, biometrics are not the only measure used by the Zengo app, so even in the unlikely event that a skilled attacker is able to bypass it, other factors will be able to stop the attack.
To address privacy concerns, our product architecture does not allow either Zengo nor the biometric provider to access any of the user’s biometric data.
Security is one of the main pillars of Zengo, and we plan to continue investing in improving the authentication experience and security for our wallet users.
