Tl;dr: Don’t be so sure that a “verified” checkmark means you’re engaging with the real deal. This is a major Web3 user vulnerability. We share our discovery, and suggest potential ways to fix it.

As part of our ongoing research in blockchain security, we have taken a deeper dive into the security of connecting to web3 dapps. Dapp connections are often the achilles heel of Web3 security, as many times attackers trick their victims into connecting to rogue dapp’ web2 interfaces.
During this research, we identified a popular wallet that was misinterpreting some fields in WalletConnect, the leading standard for mobile wallet connection to dapps, putting its users at greater risk to such attacks. We have since responsibly disclosed the issue to the vulnerable wallet, and they have fixed that issue.
In this blog, we will explain the issue in detail, demonstrate its implementation by the vulnerabile wallet, and share some practical security recommendations any user can follow to watch out for similar pitfalls.
The Web3 Triangle: Web2 interfaces and WalletConnect
Web3 allows users to perform complex operations by sending on-chain transactions to Smart Contracts through dapp. For example, users can send a transaction to exchange a certain asset for another asset under some requirements (e.g. rate has not deviated). But how would the user know how to code this complex message, which is not standard, and changes between different dapps?
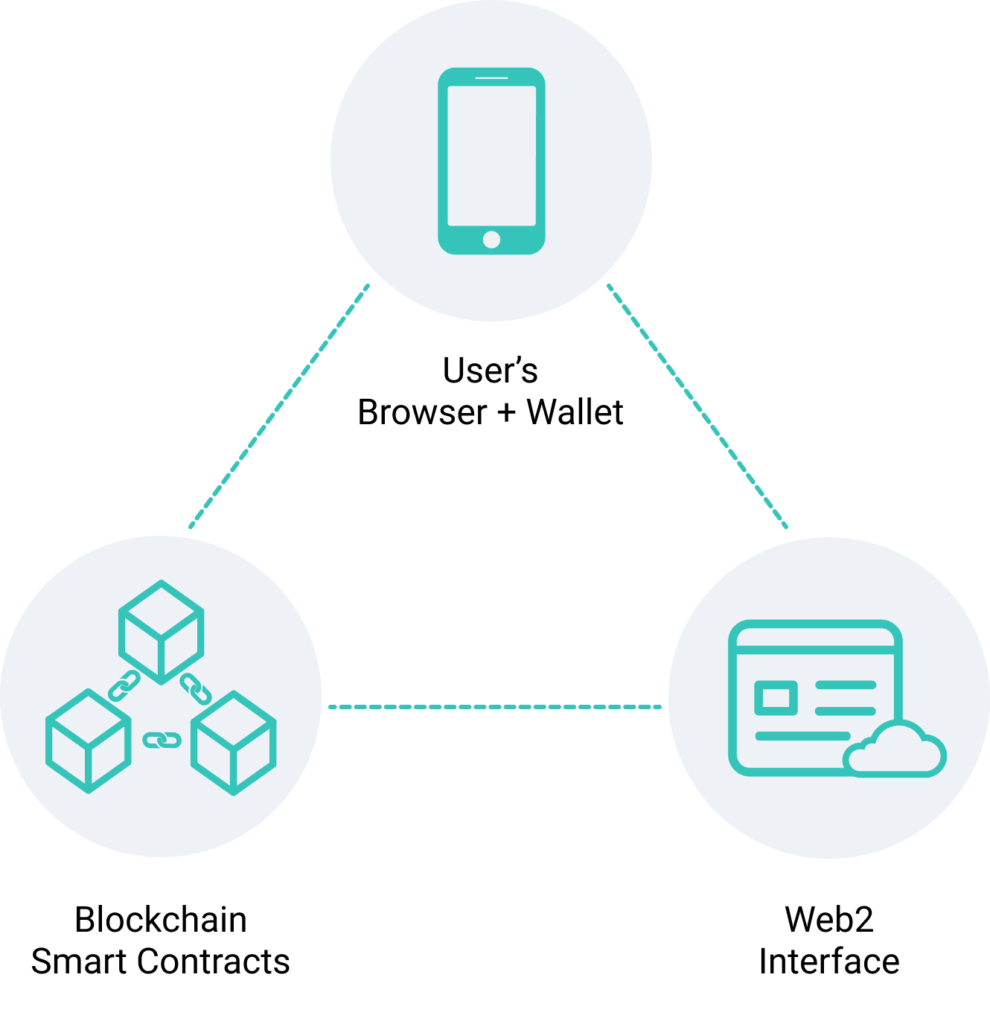
To solve that, Dapps have a web2 interface that sends properly formatted transactions to the wallet, such that the wallet’s owner can send them. This connection between the wallet and the Dapp’s interface is currently implemented mostly via either browser extension or WalletConnect for mobile wallets.
With WalletConnect, users scan a QR code with their wallet to create the channel between the wallet and the dapp. The dapp sends some information about itself (e.g. name, icon) and following that all kind of messages to be signed. Learn more about this process here.
Obviously if the dapp sends malicious messages and the user signs them, many bad things can happen. For example, the dapp can send a message that transfers all of the users’ funds to some address. Therefore, it is important for users to work with trustworthy interfaces. Conversely, attackers try to masquerade as trustworthy dapps in order to trick innocent users.
The Issue
It’s very tempting to solve the problem of dapp trustworthiness by reassuring users they are interacting with “the right” dapp based on the data passed by WalletConnect. And that’s exactly what a popular mobile browser did. When they get the URL (“address”) of the dapp from WalletConnect they present a blue checkmark, in case it’s a known site.
However, WalletConnect data is sent by dapp and cannot be validated by WalletConnect. Therefore, a rogue Dapp can claim it’s actually a well known Dapp (e.g. “OpenSea”) and this popular wallet’s users will be even more reassured that they are interacting with the real “OpenSea” dapp. After all, it has a blue checkmark!
This is exactly what we had demonstrated in the following video:
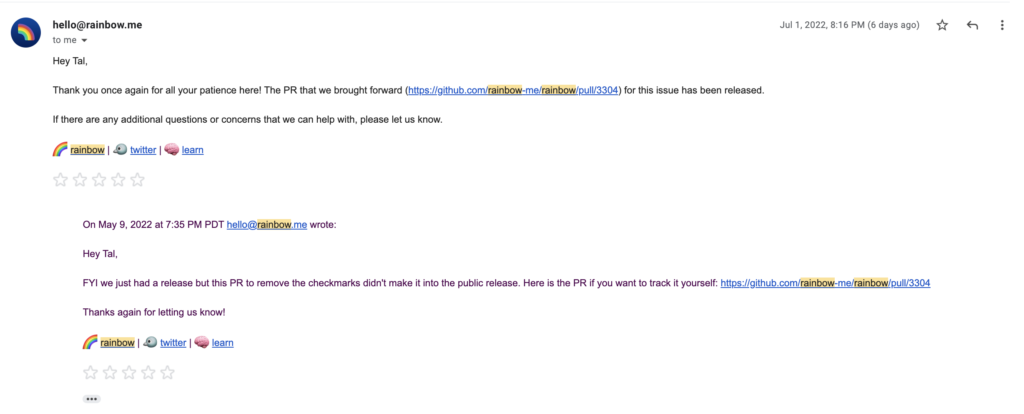
We had shared our findings with the wallet, and they were very responsive in correcting this unsafe behavior (see https://github.com/rainbow-me/rainbow/pull/3304 )
Recommendations
Users should verify on their browsers that they’re accessing the “right” dapp and not a phishing one. They can do so by
- Verifying the site address in the address bar is as expected
- The website should be served over SSL (padlock icon is present)
Additionally, users should use wallets that offer some extra layers of protection against rogue dapps, such as Zengo’s ClearSign!
Always stay alert and take steps to make your web3 journey safer!
