Tl;dr: Zengo’s research arm discovered a critical vulnerability in the popular Bitclout app, powered by the social blockchain DeSo that could have resulted in the short-term crash of the DeSo coin and potential theft of millions of dollars. The vulnerability was coined “Griphook,” after the Harry Potter goblin that assisted with a break-in into Gringotts, the novel’s central bank (and name for DeSo’s vault).
Zengo X, Zengo’s research arm, discovered a critical double spending vulnerability in BitClout, an app built on DeSo, the high-profile social blockchain with a market cap of roughly $1 billion. The vulnerability, known as Griphook, put millions of dollars at risk and could have collapsed DeSo’s price in the short-term. The discovery, led by Senior Researcher Matan Hamilis, was immediately disclosed to DeSo and has been fixed. DeSo has since awarded Zengo its highest bug bounty ($75,000) for the responsible disclosure of such a critical vulnerability.
Ultimately, this Zengo-DeSo success story exemplifies best-practices for bug bounty implementation. Zengo credits DeSo’s leadership for their proactive efforts in establishing a transparent bug bounty program and quickly working with Zengo X to address critical vulnerabilities when discovered.
This brief post will discuss the vulnerability’s root cause, implications, and fixes. This post will not detail how the vulnerability was exploited. Find our technical, in-depth post here.
Summary
As a multichain, non-custodial crypto wallet, we at Zengo are always on the lookout for interesting projects, assets, and chains to potentially work with. DeSo (also known as Bitclout) showed early on our radar and we were interested in discovering how its blockchain operated.
DeSo, the blockchain project behind BitClout, is a blockchain focused on enabling Web 3.0 social apps. Like a decentralized Twitter, every user can mint individual creator coins on the platform, which adjust in value based on demand and other factors. The DeSo coin is the base currency supporting all underlying network transactions.

Figure 1. DeSo’s Homepage
In order to on-ramp to the DeSo network, DeSo established a BTC-DeSo bridge that allows users to swap Bitcoin for DeSo coins. After a trade is completed, DeSo coins are immediately transferred to the user, even before the Bitcoin network successfully mines the Bitcoin transaction into a new block. This was a shortcut taken to enhance user experience, instead of waiting for a few Bitcoin block confirmations, as is best-practice applied by exchanges, wallets, and most crypto companies.
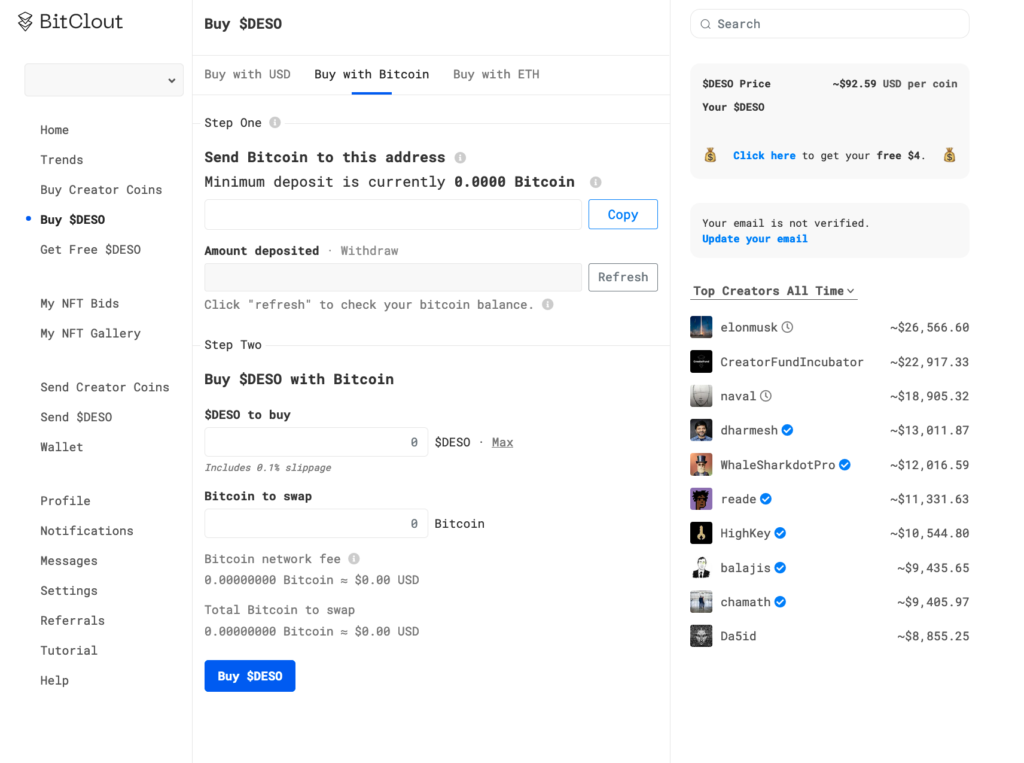
Figure 2. BitClout’s BTC-DeSo bridge page
To prevent any obvious double spending attacks, which would allow a user to receive new DeSo coins and keep the original Bitcoin payment, DeSo’s system implemented various preemptive checks against any transaction. One of the most important preemptive checks was conducted using BlockCypher, a popular blockchain explorer that provides real time updates on Bitcoin transactions that offers an API to detect double spendings in Bitcoin.
Understanding Griphook: The vulnerability’s root cause
The Griphook vulnerability was found in the gap between DeSo and BlockCypher’s interpretation of double spending. Double spending is the act of broadcasting two different transactions to the Bitcoin network where both transactions spend the same set of coins: Think of it like giving the same $10 dollars to two different people. In the physical world, that is not possible. In the virtual world, Bitcoin solved this problem by breaking transactions into timed blocks, like layering a new sheath of amber over a fossil every 10 minutes. With every additional layer, users can be certain that older transactions are secured. This is why it is best-practice to wait at least 2 blocks before confirming final settlement: until the amber dries, the situation remains unclear.
DeSo’s decision to confirm transactions immediately optimized for user experience, but exposed itself to vulnerabilities, which, unless sufficiently mitigated, could result in successful double-spending attacks. Griphook exploited the fact that DeSo’s interpretation of a certain double-spending-detection API by BlockCypher was not water-tight: the API does not check for double spends by ancestor transactions, leaving room for a complicated but possible exploit. By successfully exploiting this vulnerability, an attacker could trick the DeSo-Bitcoin trading bridge into sending DeSo coins without actually paying the Bitcoin, effectively draining DeSo’s crypto vault.
![]()
Figure 3. The documentation of double_spend in BlockCypher’s API.
Implication 1: Millions of dollars were at risk
DeSo coins sent in exchange for Bitcoin are sent from the DeSo user known as Gringotts Bank, a DeSo account created especially for this purpose. At any given time, this account would hold up to tens of thousands of DeSo coins, each worth ~$150 at the time this vulnerability was discovered. Therefore, emptying Gringotts’ vault would result in the profit of millions of dollars.
Moreover, Gringotts Bank appeared to automatically refill itself whenever emptied. Therefore, it is hard to estimate the total amount of money that could have been stolen, because it’s hard to tell how many times this attack might work without getting noticed.
If you are a Harry Potter fan, you can probably understand why this vulnerability was named “Griphook.”
Implication 2: Potential short-term crash in DeSo coin price
The Griphook vulnerability allowed an attacker to steal funds from DeSo’s vault (Gringotts Bank). If stolen, these coins would likely be immediately sold for Bitcoin for two reasons:
- To steal even more coins in an ever-growing loop.
- To leave DeSo with no option to revert the theft.
This exchange of large amounts of DeSo coins into Bitcoin would probably have collapsed DeSo’s market price in the short term.
It is worth noting, however: neither user funds nor the integrity of the DeSo blockchain were at risk at any point.
Suggested Fixes
One possible solution was to wait for a Bitcoin block confirmation. However, because this would not be immediate (and could take an average of 10 minutes, but sometimes longer) this would understandably result in a poor user experience.
The main suggested and implemented mitigation would 1) check with BlockCypher to ensure any current transaction is not a double spend, and also 2) confirm that any ancestor transactions of those reaching DeSo’s payment bridge are not attempted double spends: As BlockCypher does not implement this check on its own, DeSo’s servers must do so manually.
Two additional suggested (and implemented) fixes include:
- DeSo should rely on more than a single Bitcoin explorer to detect double spending attempts. While this does not eliminate the possibility of stealing funds, it makes it much more difficult to successfully implement.
- DeSo should hold less coins inside of Gringotts Bank at any given time, making any potentially successful attack much less lucrative.
This vulnerability was considered a critical exploit by DeSo, and Zengo was awarded $75,000, the highest bug bounty offered as part of their bounty program. This is a great success story and an ideal example of bug bounty implementation: Zengo credits DeSo’s leadership for their proactive efforts in establishing a transparent bug bounty program and quickly working with Zengo X to address critical vulnerabilities when discovered.
DeSo CEO Nader Al-Naji praised Zengo for adhering to the “gold standard of responsible disclosure,” saying “Not only did Zengo alert us to this vulnerability, but they also worked with us closely to develop an optimal solution that fixes it without compromising user experience.”
Now, the DeSo code is even more resilient to potential future attacks.
Find our technical, in-depth post here.
