TL;DR: We present a unique glimpse into Bitcoin money laundering practices, including a hack of more than $1.5M laundered via the Binance exchange.
A few days ago, CWT, the travel giant with more than $1B in revenue last year, was hit by the Ragnar Locker ransomware. The attackers encrypted data on CWT computers and exfiltrated some of it, threatening to expose the data unless a ransom was paid.
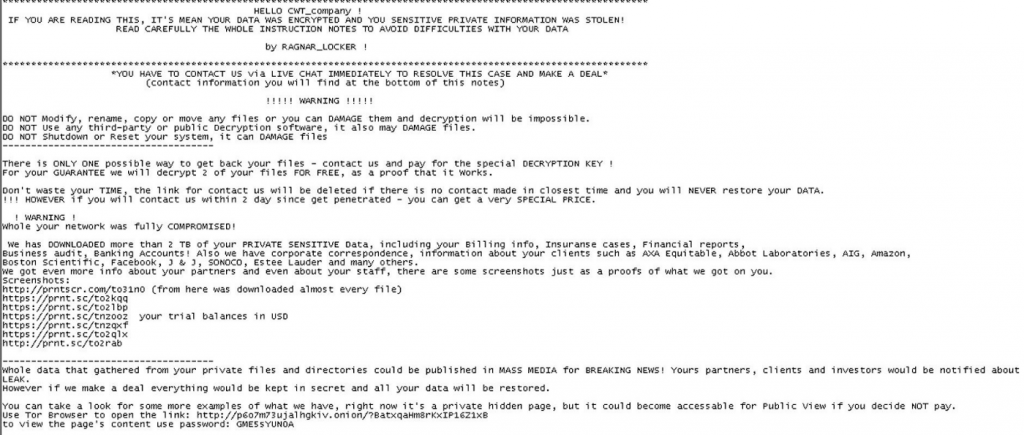
This story is not extraordinary by itself, as many companies and individuals have been hit by ransomware. However, it has a very unique angle to it. While most ransomware cases occur behind closed doors, CWT and their attackers inadvertently left the trail of their conversations open to public view, providing a unique glimpse into an otherwise secret world of ransomware-related negotiations.
A few days ago, Reuters exposed the correspondence between the parties. CWT agreed to pay more than $4M in Bitcoin (more than 400 BTC) to attackers in exchange for a decryption key to unlock their data.
In this article, we use the data from the correspondence to explore the ransomware Bitcoin money trail.
Analysis methodology
This analysis was made possible due to the pseudonymous nature of Bitcoin. While the Bitcoin blockchain does not identify its users, it allows observers to watch the transactions between these addresses as they are represented by mostly meaningless addresses.
By following the trail of transactions starting from the initial attackers’ address and using some Bitcoin intelligence services to identify and cluster known exchange addresses, we gained some insights into the underworld money transfers.
We were able to dissect the attackers operations into few distinct stages:
- The payment.
- The splits.
- The Binance laundering.
The payment
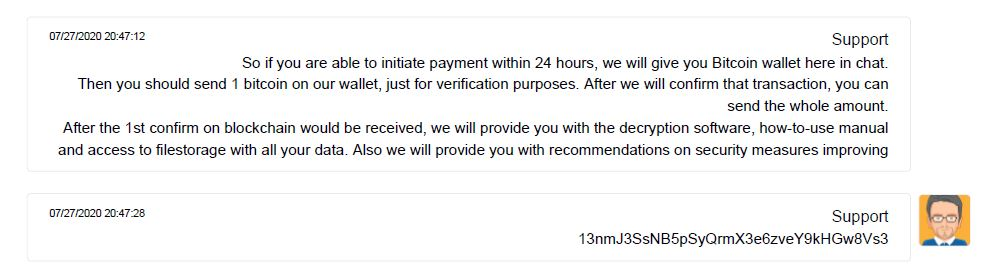
The victims purchased 414 BTC to pay the ransom. On June 27th, a few minutes before midnight (UTC time), they had sent 1 BTC out of this sum to the attackers’ address. The remainder (commonly referred to as the “change”) was transferred to a new address of the victim. The victims waited for the attackers to confirm they got the money. 20 minutes later, once the attackers confirmed the receipt, the victims sent the rest of the funds, 413 BTC, to the attacker.
The Splits
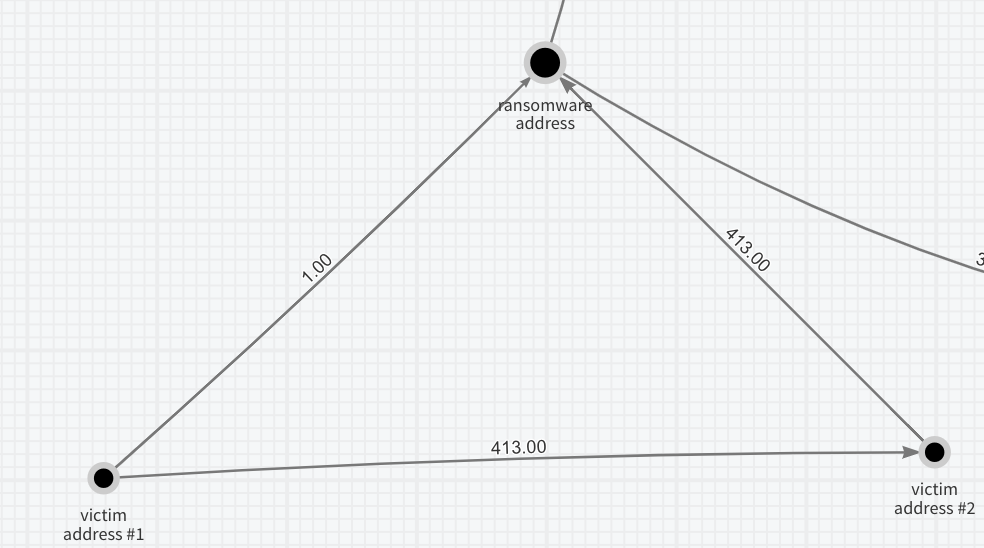
Within 20 minutes, the amount was split into two addresses from the attacker’s address, with 102 BTC to the first and 310 BTC to the other.
It seems this split was not technical in nature, but the two parties represent different functions within the attackers’ group, for the following reasons:
- Wallets: These parties are using different types of Bitcoin wallets. The first used a wallet that used a Bitcoin “legacy” address format (starts with “1”), while the second used a more modern address format (starts with “3”).
- Operation times: The first address immediately proceeded to pass the money around, while the second only acted 6 hours later (maybe located in a different time zone).
- Modus Operandi: The first address almost did not cash out through exchanges, while the second did.
The second address then split its 310BTC again to equal parts, each with 155BTC.
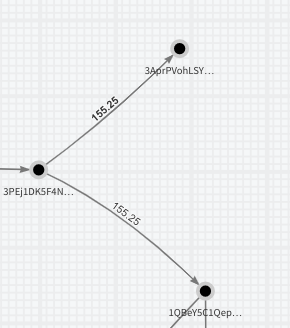
As before, note the two parties are using a different wallet technology (address starting with “1” versus “3”).
Laundering through exchange
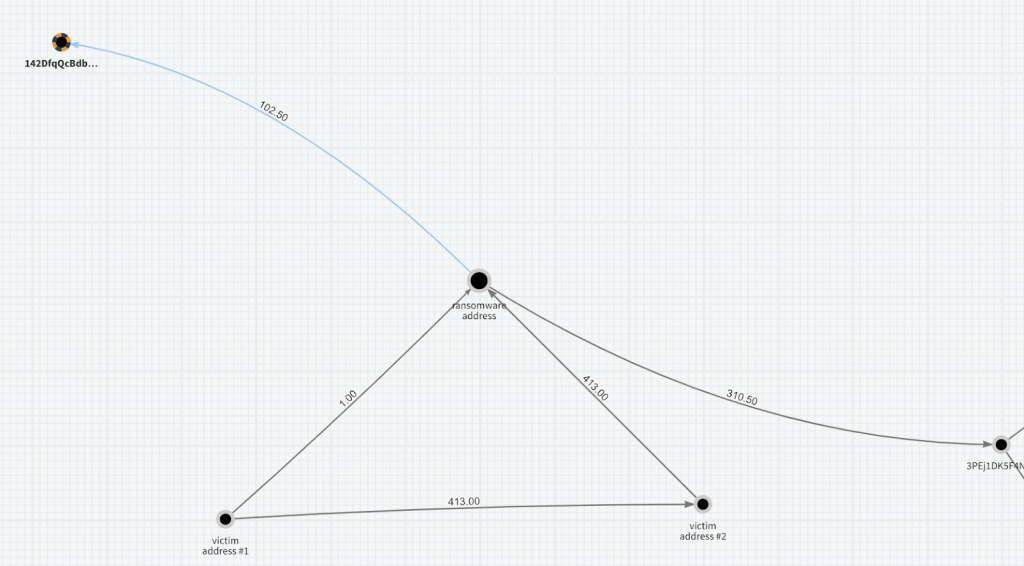
One of the parties used the Binance exchange to “launder” their 155 BTC (more than $1.5M).
Most attackers are very aware that their Bitcoin actions are not anonymous but rather pseudonymous and traceable. If law enforcement authorities identify the addresses involved, they can blacklist the addresses and prevent centralized exchanges from accepting payments.
The ultimate way for attackers to cover their tracks is to “mix” the dirty money with large amounts of clean money. The mixing is done by depositing the dirty money into a pool holding more substantial quantities of clean money from legitimate parties, and then withdrawing from the pool. Some black market mixing services exist for this purpose. However, to effectively mix $1.5M in a timely manner, a more significant source of liquidity is required.
The biggest sources of liquidity in cryptocurrency are centralized exchanges. In an exchange, “dirty” money blends with the rest of the funds held by the exchange, so when the attackers draw their money, it is laundered and cleared from its on-chain history. Additionally, the attackers can use exchange services, and get non-traceable “privacy coins” (e.g., Zcash) for their traceable Bitcoin. As all transactions done on centralized exchanges are completed privately and off-chain, they are not detectable outside of the exchange.
However, centralized exchanges are somewhat regulated and usually require their customers to go through a “Know Your Customer” (KYC) process. The level of detail involved in the KYC process, which includes all sorts of identification papers and methods, depends on a risk assessment of the transactions. Attackers can overcome KYC requirements by using stolen identities, especially for lower levels of KYC. (For a higher level, it would probably require “money mules” with real identities).
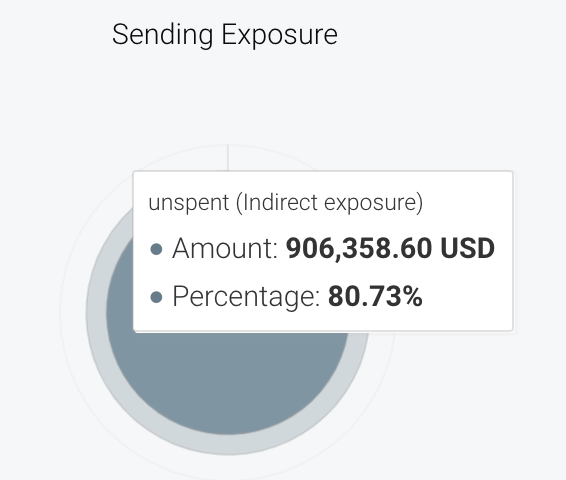
Naturally, the leading risk factor is the transaction amounts. Sending $1.5M in just one transaction would have probably crossed the exchange risk threshold and dictated a more thorough investigation into the participating parties with a more elaborate “Know Your Customer” (KYC) process. To avoid this added scrutiny, the attacker split the sum into smaller payments.
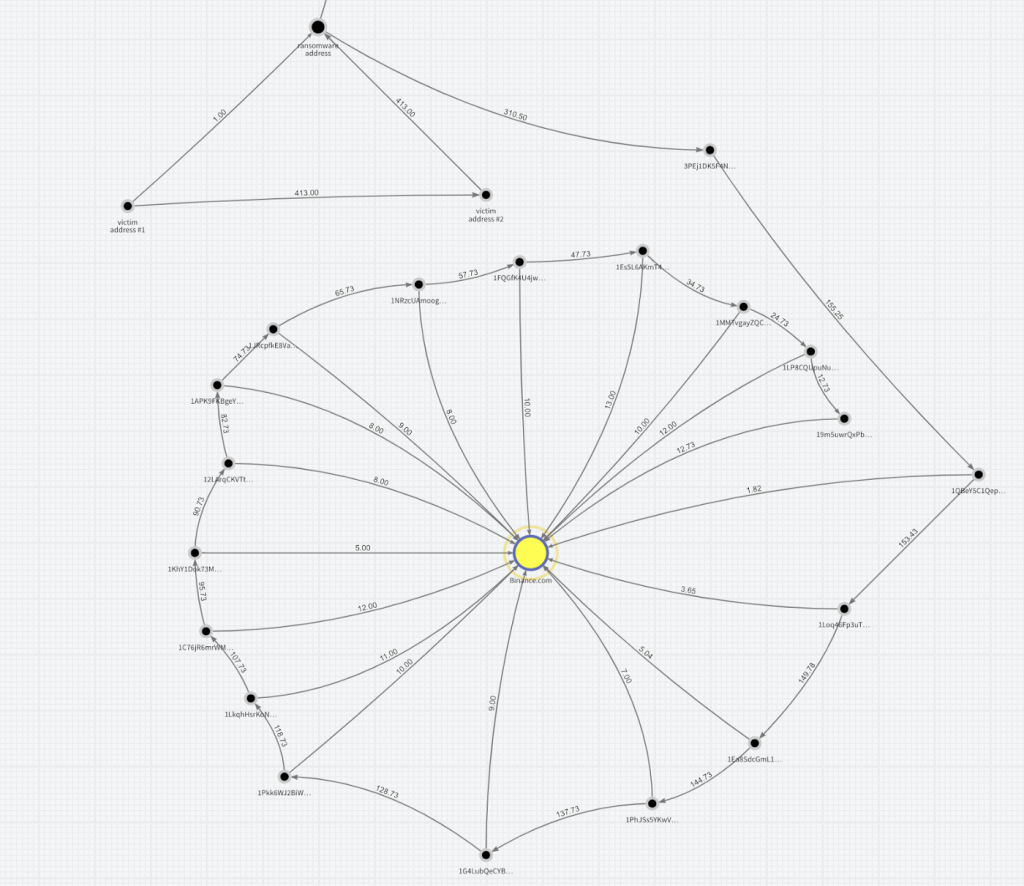
The graph above shows how the attackers split this large sum into relatively small payments (~ 10 BTC ) to the exchange (big yellow circle in the middle). Each address sends a small amount to the exchange, and the change is sent to another address controlled by the attacker. The process repeats until it’s all sent to the exchange. This analysis is not trivial and was enabled by using intelligence providers to cluster the different Binance exchange addresses into one identity.
The first transaction was sent on June 28th at 6AM (UTC), followed by a series of almost 20 transactions sent with 30 minutes to 1-hour delays between them until 9PM that night. We can see the attackers started slowly with a low amount (1.5 BTC) to ensure they are not stopped by risk thresholds and then gradually increased the amounts: 3.6, 5, 7, 9, 10, 11, 12 BTC on the following transactions.
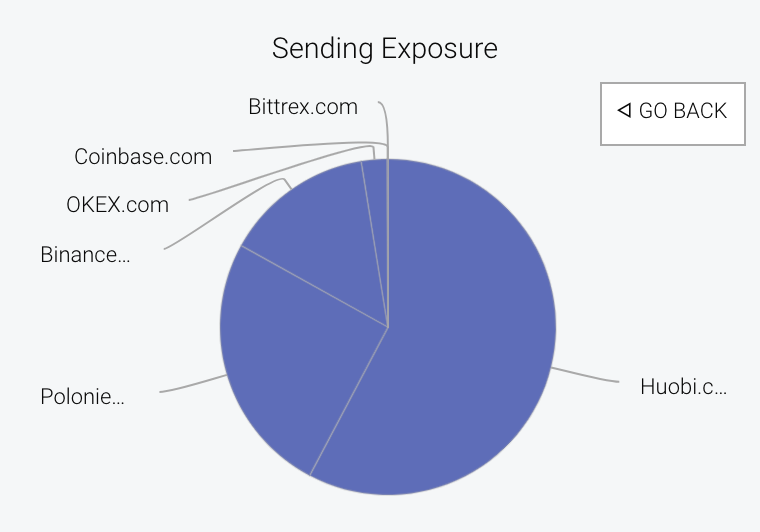
The 155BTC of the second party was sent to other exchanges (mostly Huobi) but did not show such a clear pattern.
Summing up
At Zengo, our users’ security is our top priority. That’s why we try to learn from every crypto-related security incident. We have found that observing incidents is always useful and often leads to some interesting insights. We believe understanding this incident may increase the awareness of exchanges and law enforcement bodies to detect and stop such underworld payments. We reached out to Binance and shared this information with them before publication, and we hope this will have an effect on similar incidents in the future.
